Traditionally UNIX and Linux have separate components for Directory Services, Name Resolution, Authentication, Privilege Management, Accounting and Configuration Management.
Note: I will be referring to the UNIX family of systems (Including Linux) as UNIX throughout this blog.
Directory Services on UNIX/Linux
UNIX Systems have been around for a long time. They have defined and built the Internet as we know it today, so we owe a lot of the benefits that we enjoy to the legacy of UNIX. With the birth of Linux, Open Source solutions and the penetration of virtualization technologies, the family of UNIX systems has grown exponentially.
This legacy means that UNIX systems have retained many of the challenges across the years.
Traditionally users in a UNIX system exist on:
- Locally in the /etc/passwd file
- In a Network Information System (NIS)
- In an LDAP system (like OpenLDAP)
- In commercial solutions and even in Active Directory
Because of the fragmentation of directory service providers and to eliminate having to compile programs for each provider, Sun Microsystems introduced the NSS facility. It allows programs to access directory services, name services and remote databases in a standard fashion. NSS is very important to understand how Centrify integrates with UNIX systems to provide name services via AD. The configuration for NSS is in the /etc/nsswitch.conf.
Authentication Services on UNIX/Linux
Just like Directory services, authentication in Unix has been performed:
- Locally against the /etc/shadow file
- In a Network Information System (NIS) remote shadow file
- Over a Kerberos infrastructure (like MIT Kerberos or Heimdal)
Because of the same needs around NSS, PAM is authentication framework that allow stackable modules implemented as shared objects to perform authentication functions. For example, an account module can verify is the user account is valid, the authentication module can verify the validity of the password, the session module can display a message of the day to the user. Along with NSS, Centrify uses a PAM module to authenticate against Active Directory's Kerberos implementation.
Name Resolution in UNIX/Linux
BIND is the defacto DNS server in UNIX. The client component is controlled typically via the /etc/resolv.conf file.
Privilege Management in UNIX/Linux
Shared Privileged Accounts:
In UNIX, the root account is is king. Aside from being able to impersonate any user, is able to take ownership of any file or process. It is not uncommon (even in mature regulated organizations) to see users abuse the root account. Sometimes even when a commercial solution or sudo is implemented, users will still issue a command to elevate to root. This undermines accountability.
Sharing accounts is generally considered a bad security practice.
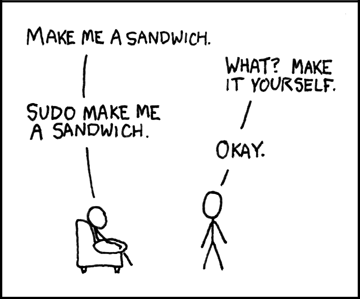
sudo
sudo is a privilege management utility that allows users to run programs in the security context of another user. It uses the /etc/sudoers file. It is prevalent and reliable.
Commercial Solutions:
There are a number of commercial solutions in the market to tackle the UNIX privilege management puzzle. We will focus on leveraging Active Directory and Centrify-enhanced sudo in this blog. Commercial solution approaches include:
- Scripting-oriented: Like BeyondTrust's PowerBroker
- Password Vaults: Like Cyber-Ark
- Kernel-level: Like CA's Access Control
The syslog facility is the main repository for logs, including security events. Interestingly, when using root in a shared account scenario, there are events that are not logged!!!!
Configuration Management on UNIX/Linux
Traditionally, configuration management has been accomplished with scripts written by system administrators, but this approach may not scale depending on the core competency of the company. Companies like AOL, Google and others are pure tech companies and writing software is their core competency; but banks, insurance companies, manufacturing companies, etc may not have the same luxury. Wikipedia has a great article on Configuration Management utilities for UNIX and Linux like Chef, Puppet, etc.


Great Content. It will useful for knowledge seekers. Keep sharing your knowledge through this kind of article.
ReplyDeleteUnix Training in Chennai
Linux Training in Chennai
ReplyDeleteNice blog! Thanks for sharing this valuable information
Cyber Security Course in Pune
Cyber Security Course in Gurgaon
Cyber Security Course in Hyderabad
Cyber Security Course in Bangalore
cyber security course in delhi
cyber security course in kochi
cyber security course in ahmedabad
cyber security course in mumbai